In the interest of openness, the WikiLeaks successor DDoSecrets has gathered a contentious new collection of business ddosecrets wikileakslike 1tbgreenbergwired.
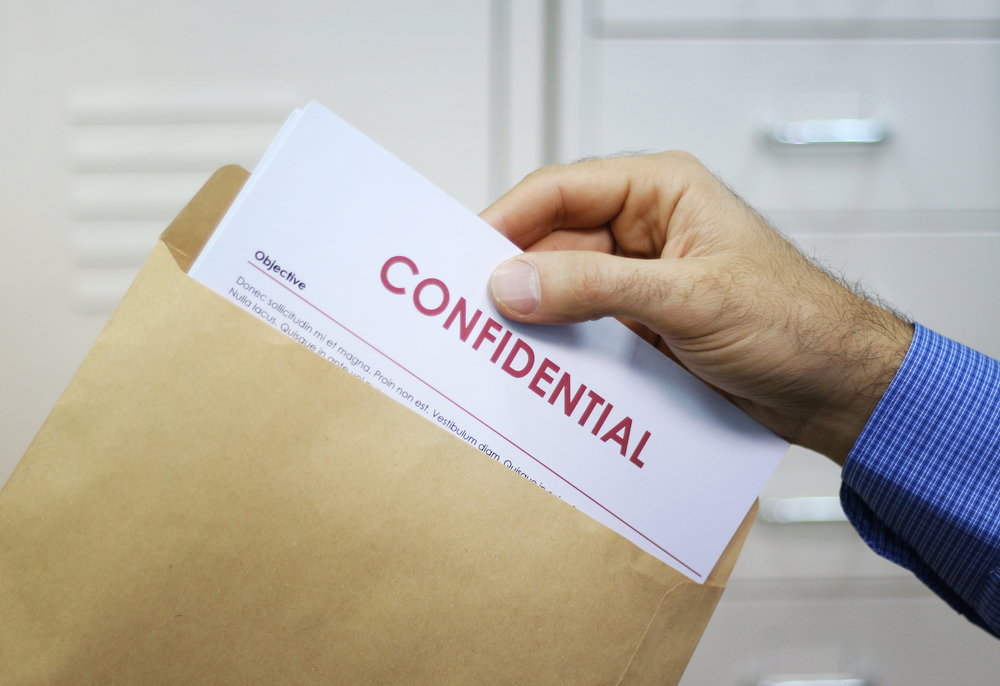
Radical transparency advocates like WikiLeaks have been fusing hacking and whistleblowing for years. No matter how dubious the source, they frequently publish any data they deem to be of public importance. However, one leak-focused organisation is currently mining a contentious new source of information: the enormous data caches that ransomware teams steal and release online when victims refuse to pay.
The transparency group of data activists known as Distributed Denial of Secrets today released a sizable new amount of data on its website, all of which were gathered from dark web sites where the material was initially disclosed online by ransomware hackers. About 1 terabyte of the information, which includes more than 750,000 emails, pictures, and documents from five companies, has been made public by DDoSecrets. With selected journalists or university researchers, the organisation is also offering to confidentially share an extra 1.9 gigabytes of data from over a dozen other firms. The massive data gathering covers a wide range of businesses, including manufacturing, finance, software, retail, real estate, and oil and gas.
All of that data, along with the gigabytes more that DDoSecrets claims it will provide in the upcoming weeks and months, comes from a trend among ransomware operations run by cybercriminals that is becoming more and more widespread. Ransomware hackers now frequently steal huge quantities of victim data and threaten to publish it publicly unless their hacking targets pay, going beyond simply encrypting victim PCs and demanding a payment for the decryption keys. The victims frequently reject that extortion, and the cybercriminals often carry out their threat. As a result, dozens or even hundreds of terabytes of private corporate information are exposed and posted on dark web servers, the web addresses of which are known to hackers and security experts.
Co Founder of DDoSecrets
Emma Best, co-founder of DDoSecrets, asserts that the data dump trails that ransomware operations leave in their wake frequently contain information that should be examined and, in some cases, made public. In a text message discussion with WIRED, Best said, “Ignoring critical data that can educate the public about how companies operate isn’t something we can afford to do.” Given that there is too much data for DDoSecrets to look through on its own, Best, who uses the pronoun they, was unable to state in many instances with certainty what secrets of possible public interest those enormous data sets may contain. But they contend that any proof of corporate wrongdoing revealed by those records, or even intellectual property that can benefit the public, should be regarded as fair game.
According to Best, “we have a duty to make that information available to researchers, journalists, and scholars so they can learn about how typically opaque industries (many of which control significant aspects of our lives and the future of the planet) operate.” This could be a pharmaceutical company, a petroleum company, or any other business with technical data and specs.
Exploiting data leakage left behind by cybercriminal hackers, however, raises significant ethical dilemmas for those battling the spreading global scourge of ransomware attacks. In his opinion, amplifying the leaks from ransomware groups only encourages them to threaten those leaks against more victims. Allan Liska is an analyst and researcher for the security firm Recorded Future. He claims to have personally witnessed the devastating effects of ransomware attacks on businesses of all sizes. Personally, I believe it to be incorrect, says Liska. “I believe you are taking advantage of someone who has a crime committed against them, even if you believe your motives are good,”
The best defence is that DDoSecrets isn’t disclosing any information that those hackers haven’t already made available. They claim that all of the information was previously published by ransomware hackers. “We don’t collaborate with them in any manner or receive anything from them directly. We are making data available that journalists are unable or frightened to access. Best adds that DDoSecrets will often discuss the majority of the leaks in private with journalists and scholars rather than publishing the material themselves. In those circumstances, they will request that anyone publishing the data redact anything that is excessively sensitive and doesn’t serve the public interest, including personally identifiable information. However, if the organisation decides that revealing such private information would be in the public interest, they reserve the right to do so. They also intend to grant the journalists and academics they share data with the same freedom to publish their findings.
DDoSecrets further points out that, whether or not it obtains personally identifying information, cybercriminals who might use it in ransomware leaks are already searching those breaches. The bogeymen that everyone enjoys worrying about? best authors. “They already have the information.”
Best cites the instance of Perceptics, a company that makes technology for license-plate readers. Perceptics experienced a breach in the spring of last year, and as per tech news site the Register, a ransomware hacker likely released its files onto the black web. In order to demonstrate how Perceptics had lobbied Congress for Customs and Border Protection contracts and downplayed security and privacy issues with its tech—even as the delicate license-plate data it was collecting was left vulnerable to hackers—journalists at the Intercept dug through the leaked data.
We cannot afford to ignore important data that can educate the public about how various sectors function.
BEST, EMMA; DDoSecrets
DDoSecrets released their own explosive collection of breached documents in June of this year. The group received BlueLeaks, a sizable collection of law enforcement information, from a hacker affiliated with Anonymous. The DDoSecrets account was suspended by Twitter, and all tweets including links to its website were even blocked, as a result of the 269 GB collection of papers from 200 state and local police organisations. The r/blueleaks subreddit was blocked by Reddit. Shortly after, DDoSecrets suffered a huge setback from which it is still trying to recover when German prosecutors in the town of Zwickau ordered police to take a server belonging to the organisation that housed many of its files and the search engine for its data gathering. It now intends to store its data on Tor-protected.onion sites that conceal the physical location of servers, making future seizures much more challenging.
DDoSecrets is still committed to completing its bigger objective in spite of those obstacles. It has also tapped into a large new stream of leaks thanks to its new malware trove. According to Liska of Recorded Future, more than 1,000 ransomware victims had their data leaked onto dark web sites just last year. He calculates that the total amount of stolen data posted to numerous dark web sites during a single year of ransomware outbreaks is between 100 and 200 gigabytes.
Sign up for the Fast Forward newsletter to receive the latest news on everything from self-driving cars and artificial intelligence to newly launched enterprises and altered cities.
that email
Type in your email.
SUBMIT
By registering, you consent to our User Agreement, which includes the arbitration and class action waiver clauses, as well as our Privacy Policy & Cookie Statement. You also consent to receive communications from WIRED about marketing and your account. You are always free to unsubscribe.
According to Thomas Rid, a professor of strategic studies at Johns Hopkins University who wrote extensively about hack-and-leak operations in his book Active Measures, the ethics of searching through that deluge of leaked data for information of public interest is dependent on more than just whether the data was leaked by an insider or stolen by a hacker, or even the intentions of whoever might have stolen it. It would be significantly different from WikiLeaks’ widely criticized decision to release previously unpublished emails taken from the Democratic National Committee by Russia’s military intelligence agency in 2016 if the data had actually been made public by hackers prior to DDoSecrets obtaining it.
In an auto repair shop, the most popular car technicians’ tools are hung on a blue wall.
HIGH-TECH CARS: The Death of the Auto Repair Shop
MARCIAN AARIAN
smartphone Samsung Galaxy Note 20 Ultra lying on a white table against an orange background.
DAVID NIELD’s GEAR 19 Android Settings You May Not Know
The 12 Best Electric Bikes for All Types of Riding
DARRENNE SO
a person reading a book while curled up with a grey blanket on a grey couch
The 15 Books You Must Read This Fall, According to CULTURE WIRED’s Picks WIRED STAFF
ADVERTISEMENT DDoSecrets
But Rid points out that DDoSecrets’ decision to keep the data forever is more morally dubious because, in many situations, the material may only be accessible on a dark web site for a little period of time. When you are the sole source, Rid explains, “you are essentially the publisher at that point.” “These ethical edge scenarios must be acknowledged by Emma and their colleagues. They cannot simply act as though they are not in uncharted territory.”
Best claims that ignoring the existence of ransomware data merely permits hackers to take advantage of it, leaving its value as a source of newsworthy muckraking or other benefits to the general public. Terabytes of data are “inundating the dark web and being utilised almost exclusively by hackers and the kind of people security experts and commentators love to wring their hands over,” says Best. “But they’re virtually wholly unavailable to the public and to journalists.” Our main objective has always been to help and inform the people.